Hack The Box: Traverxec
Synopsis: Traverxec is a Linux machine running a nostromo web server. A quick google or searchsploit tells us that version 1.9.6 is vulnerable to a RCE vulnerability that has a metasploit module. Using metasploit allows us a foothold on the system as the www-data user. To elevate privileges a backup file for the user David can be found in the /home/david/public_www/protected-file-area directory. After using netcat to move the file back to kali to work with it we can use John to decrypt the file and locate david’s password. This allows us to ssh as david to the machine and grab his flag. From here we perform a shell escape sequence on journalctl with the aid of gtfobins giving us root access and the ability to grab the root flag.
Port 80 jumps off the page with an odd webserver
searchsploit tells us there is a metasploit module for this version of Nostromo
got a shell but with next to no privileges. boo
David leaves valuable files lying around with passive aggressive notes.
Lets move it back to kali to work with it.
unpack the file and view the key
Use john to hash the rsa key and run it through the rockyou wordlist to find out what david’s password is.
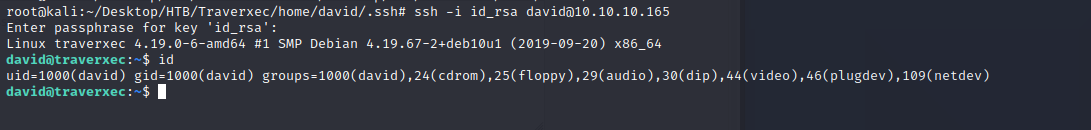
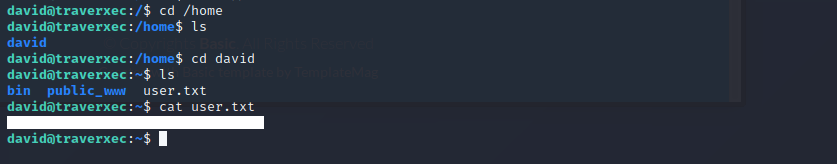
Using the information above we can now ssh as David and grab the user flag.
This is the tough bit we can view the script and use a shell escape sequence to elevate our privileges.
gtfobins is a great cheat sheet for this. If I hadn’t just taken the Ti3beriu’s linux privilege escalation class I would have been very lost. My cheat sheet can be found here.
Got root and grabbed the root flag.