Hack The Box: Devel
Synopsis: Devel was a great windows box that needed a lot of different skills to exploit. The need to create a reverse shell and then elevate privileges made it a great learning experience. It also hammers home why you should never have anonymous ftp enabled.
Nmap to find out what we have to work with. I noted anonymous ftp and the IIS server immediately.
Checking out what is on port 80 confirms this is a Windows IIS server.
Based on what was listed in the anonymous FTP I pulled up file file “welcome.png” over http. At this point I knew remote code execution was going to be the way in.
While I knew the theory of reverse shells I had never actually created one. It took some research but I was able to learn how this is achieved. The above command was run on my machine to generate a the shell script. It was at this point I leaned on ippsec for help.
In this case I needed the filetype to aspx. So I adjusted the commands appropriately.
I went ahead and started a listener to listen on the appropriate port.
I then went over and uploaded the reverse shell I created via anonymous ftp.
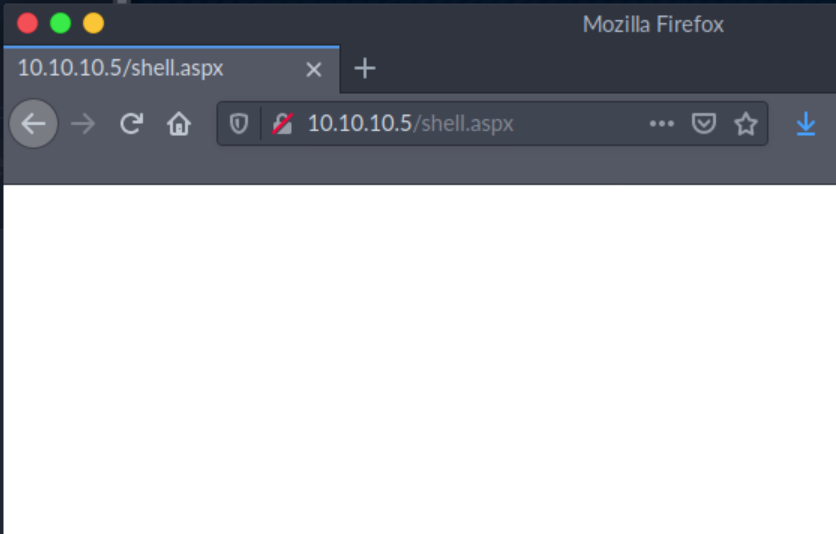
I executed it by trying to open it in the web browser.
Bummer I became a user with no privileges. Another opportunity to practice privilege escalation.
I dropped out of the shell and back into metasploit to find a way to elevate my privileges.
BAM. Im system. Now its just a matter of grabbing the flags.
I like this box a lot because it had me demonstrate/learn a lot of different skills. In particular I learned how to create reverse shells.